Executive Summary
SEC.01TorZon Darknet operates as a hidden service marketplace within the decentralized Tor network. Established to facilitate peer-to-peer commerce through cryptographic protocols, the platform primarily centers on the exchange of digital commodities, bespoke software, and privacy-centric services.
From an analytical standpoint, the architecture represents a mature iteration of hidden service deployment. The infrastructure is designed to obscure geographical hosting locations while utilizing robust cryptographic enforcement to mediate interactions between anonymous participants. Observers note that its systematic approach to operational security has made it a subject of extensive study regarding darknet commerce resilience.
Historical Timeline
SEC.02Infrastructure Genesis
Initial routing nodes were established to test server load structures. The basic framework for database synchronization and peer routing was finalized, ensuring the hidden service could withstand moderate traffic spikes.
Cryptographic Integration
Implementation of mandatory PGP standardizations. The platform transitioned to a purely encrypted communication framework, disabling plaintext metadata options for dispute resolution.
Network Expansion
Deployment of multi-node redundancy mechanisms. Anti-DDoS layers were overhauled to distribute automated scraping attempts across decentralized proxy endpoints, improving uptime metrics dramatically.
Technical Architecture
SEC.03The ecosystem's structural integrity relies heavily on mathematically enforced trust systems. Researchers have mapped the primary components governing value transfer and communication flow.
Multisignature Escrow
Employs a 2-of-3 multisig framework where funds reside on the blockchain rather than in central platform wallets. This drastically reduces the attack surface for centralized fund seizure.
PGP Enforced 2FA
Access to profiles requires decrypting dynamic strings encrypted with the user's registered public key. This prevents unauthorized access even in the event of compromised credentials.
Monero (XMR) Integration
The platform operates with a strict preference for Monero, utilizing ring signatures and stealth addresses to obscure the origin, destination, and amount of all internal value transfers.
Walletless Mode
Direct-to-address payment routing circumvents the necessity of maintaining internal platform balances, further negating risks associated with hot-wallet vulnerabilities.
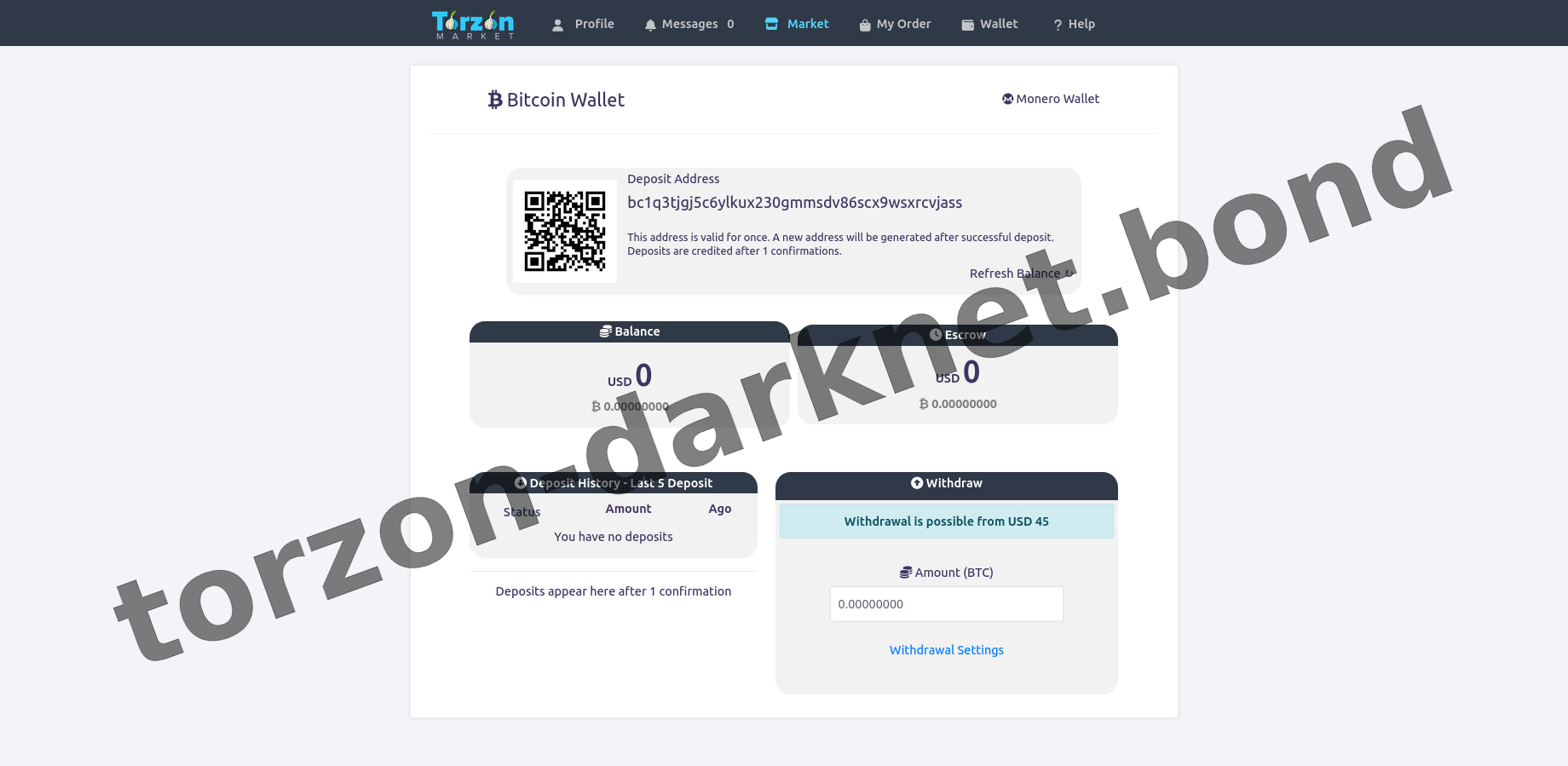
Platform Interface Preview
SEC.04Archival captures of the operational layout. These artifacts highlight the utilitarian design philosophy prioritized by the administrators—favoring rapid load times over complex visual styling over hidden network circuits.

DDoS Protection Screen - Captcha validation layer ensuring human interaction before routing to origin servers.

User Login Interface - Secure authentication portal demonstrating PGP string input fields.

Account Registration Page - Credential creation process illustrating cryptographic key binding.
Main Market Dashboard - Central navigation hub displaying catalog categorization and profile metrics.
Community & Statistical Data
SEC.05Estimated User Base
Analytical models indicate steady growth, with a highly active concurrent user count engaging across the decentralized node network daily.
Merchant Verification
Storefronts are subjected to stringent bonding requirements. Initial deposits are locked in escrow to penalize malicious activity and establish trust.
Node Uptime Metric
Maintained reputation for stability. Aggregated data from public monitoring scripts shows a highly resilient response to external network pressures.